How Do Phishers Get Email Template
Adept one-time e-mail isn't the sexiest offering in the digital globe, merely amid a whole bunch of newer apps and services — the instant messengers, the social networks — it's standing its ground equally an essential tool for modernistic-mean solar day life. About of u.s.a. withal have to utilise e-mail, at the very least to be able to register new accounts for all those services, apps, and social networks out there.
That need is exactly why electronic mail logins are a coveted prize for attackers. In this mail we'll explain how some crooks use phishing to become hold of them.
Phishing letters — the most common email hacking tactics
The vast majority of scam letters made to steal e-mail login names and passwords await like letters originating from the services we utilise for email. When targeting home users, phishers mimic popular webmail services. And when attempting to hack corporate accounts, they pretend to be your work e-mail service — in this case the sender is just the mail service server.
Popular mail services are imitated much more than often. Scammers endeavor to make such letters as disarming equally possible. The deception toolkit is the standard i: a sender's address that looks much like the existent one, logos, headers and footers, links to official resources, a plausible layout, etc.
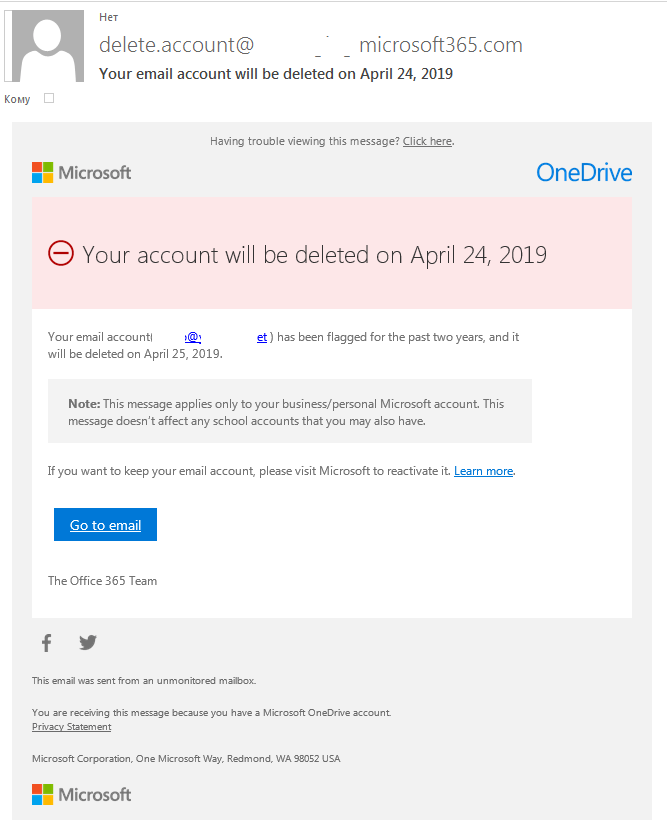
Phishing letter frightening user with account deletion
As for the corporate accounts, scammers frequently send phishing messages disguised as messages from corporate server or public email services to shared addresses (including those used by administrators), but sometimes such messages reach the mailboxes of private employees whose addresses take somehow ended up in spam databases.
Companies that want to exist taken seriously, large ones in particular, maintain email servers of their own. The logins and passwords for such accounts are also highly-seasoned to attackers. Their letters are frequently betrayed by less-than-perfect appearance — sender addresses from free webmail services, spelling errors, etc. — only fifty-fifty such letters may be taken by inexperienced employees for the real thing.
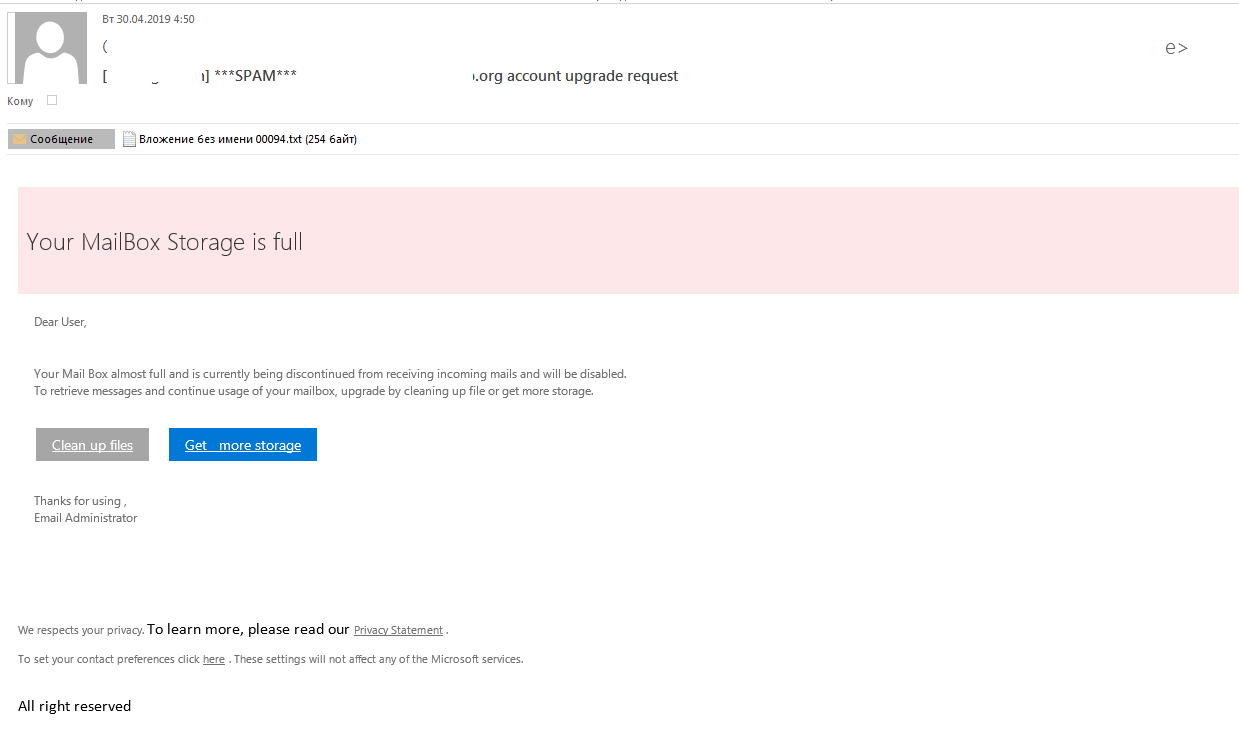
In this letter an exceeded quota alert is imitated by phishers
In case of targeted attacks on a specific organization, the scammers ordinarily collect every bit much information almost it as they can in advance to brand their letters as convincing equally possible. For a bear upon of credibility and uniqueness, they may build the victims' email addresses into phishing hyperlinks, and so that when the fake folio is visited the address is already there, and only the mailbox countersign remains to be entered.
Phishing letter variants
Simple text with request for information
Scammers simply contact users on behalf of mail services on various pretexts and request users send them e-mail addresses, passwords and other information. Users are usually urged to respond to an electronic mail address that is different from that of the sender.
This phishing letter blazon was popular enough until scammers mastered more effective personal data theft methods.

Phishing letter with a text request for business relationship data, including password. Never send anything in response to such requests
Letter with a link to a phishing website
Phishing messages with links are currently the most common type. Scammers may use infinite numbers of pregenerated links, shuffle them from letter to letter of the alphabet in the same mail blast, create phishing pages that announced very much like legitimate ones, and automate drove and processing of stolen data.
Just those links conspicuously beguile a scam, leading to domains totally unrelated to the purported organizations, or using misspelled domain names styled to look like the legitimate ones. That's why intruders try to conceal the addresses their links lead to. They do so by using clickable, hyperlinked text or images. Such text links may include phrases similar "Update your mailbox." In other cases, the text office of the link will feature the real mail service address, while the actual link will directly user to a phishing website. Many users won't see the departure unless they bank check the links earlier clicking.

About phishing messages incorporate links to phishing pages — avoid using those links
Phishing attachments
Phishing messages may also comprise attachments — typically HTML, PDF, or DOC files.
Attachments in Medico and PDF formats ofttimes contain both the torso of the phishing bulletin and the scam link. Attackers opt for this tactic when looking to brand the actual text of the alphabetic character itself as short and as much like legitimate correspondence as possible to bypass spam filters.

Some phishing letters come up with PDF or Medico attachments with links to phishing sites inside the attached file
HTML files are used instead of links — the HTML attachment is in fact a fix-made phishing folio. From the scammers' point of view, the reward is that the attached HTML file is fully functional — no need to post it to the Cyberspace — and has all the elements they need for the scam.
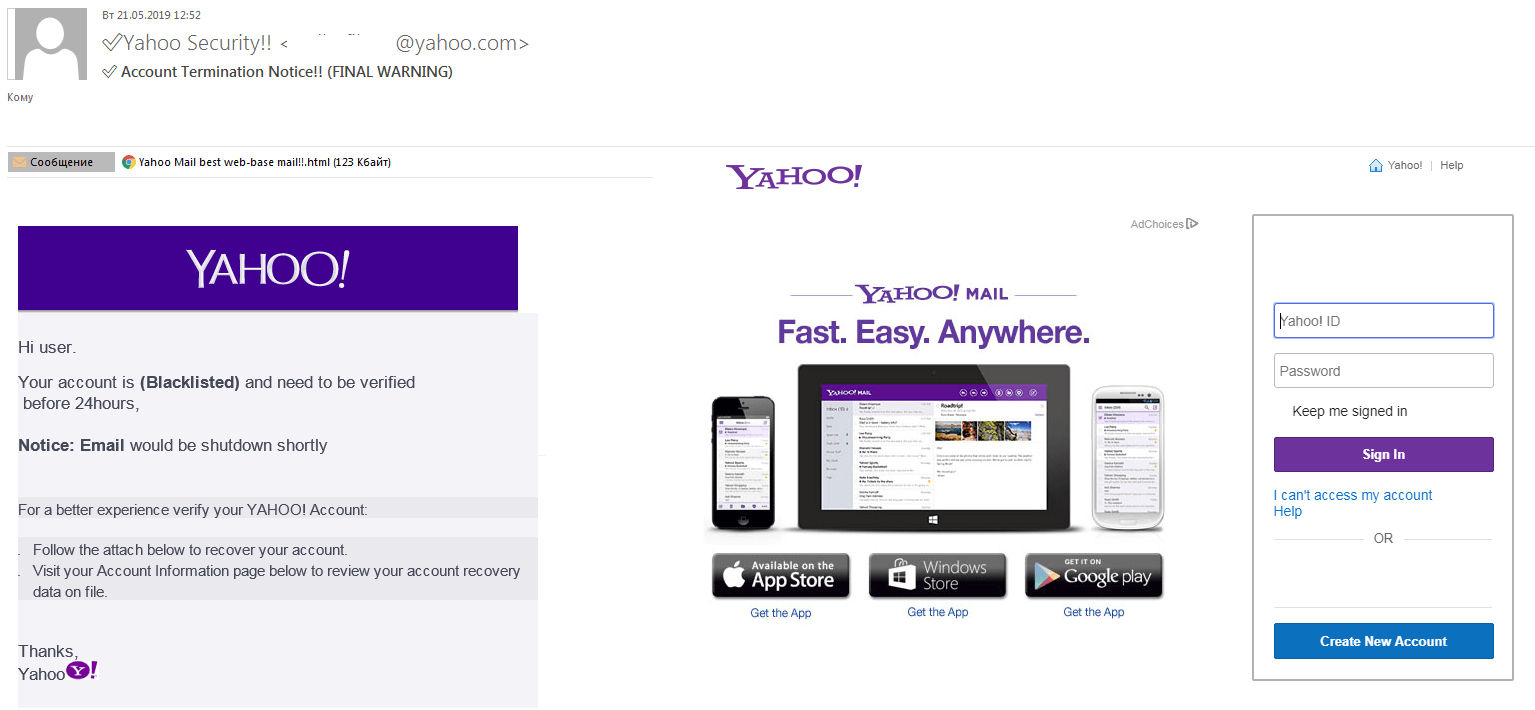
The login/password entry form is contained in the phishing letter itself. Never enter anything into something like this
Topics of phishing letters
Business relationship issues
As regards the text of the letters, almost of them brainstorm by suggesting at that place is a problem with the victim'due south eastward-mail account: storage limit reached, letter delivery trouble, unauthorized login, spamming accusations, alerts of other violations, then forth.
The letter of the alphabet normally tells the user how to deal with the trouble — by and large by confirming or updating account data by post-obit a link or opening an attachment. To frighten the recipient, it says if they don't follow the instructions, the account will be blocked or deleted.
In almost every instance, the alphabetic character sets a time frame for response, somewhere from several hours to several weeks. Usually, it's 24 hours — both apparent and not long enough to allow the victim relax and forget most the letter.

"Your account will be deleted within 24 hours due to spamming." Threats and time limits are typical phishing tricks
Imitation of business correspondence
Sometimes, singular phishing letters target e-mail accounts. The text of such letters may make no reference at all to email or account information. The alphabetic character may look quite like real business concern correspondence.
Nosotros should mention that the volume of fake business messages used for phishing has grown in the past few years. Messages of this type are normally used to evangelize harmful attachments, but some of them as well phish for personal information. A regular user may accept a hard fourth dimension detecting a phishing letter — cybercrime counts on that.

When hunting for corporate accounts, using faux business organisation correspondence is a common tactic
Some users will never suspect the fraud and volition follow the link to log in and view a nonexistent document.

Phishing website prompts user to sign in to view a document referenced in the phishing letter
Phishing page variants
At present that we are washed with the format and content of letters, let united states of america see what phishing webpages may wait like and speak about the elements to pay attention to so yous tin can detect fraud.
The start affair deserving shut attending is the link address. The address can beguile a scam correct abroad. Typical signs of fraud include:
- domains unrelated to the sending organizations,
- organization or Web service names in the address path instead of in the domain, for example, www.case.com/outlook/,
- spelling errors,
- strings of random symbols in the link address,
- symbols from other languages that expect similar to the basic Latin alphabet — ç instead of c, á instead of a and so forth.
Just as with letters, phishers try to make faux webpages as much like the real ones every bit they can. Only details always get left out — although unfortunately, not all users are able to see them.
That part is easy to understand; few people retrieve the exact appearance of the official homepage of their online services. So, to create a convincing phishing folio it is often enough to use primal characteristic elements: color scheme, logo, etc.

Fake webmail sign-in page
For phishing pages designed to steal costless webmail logins and passwords it is typical to feature links to several webmail services on the same folio.
As soon as whatsoever of them is clicked, a window pops upwardly that looks like sign-in folio for the relevant service. In this way, scammers can collect data for several kinds of account using only ane page, rather than creating separate pages for each.

This phishing website fakes logging in using different webmail accounts
Phishers can reach even more potential victims by, instead of pretending to represent a specific mail service service, using letters (on any general field of study, for example, the aforementioned business correspondence option) that link to a phishing page with a choice of the virtually popular webmail services for users to pick the ones they demand.

Another instance of a fake webmail sign-in folio
The time-limit trick we mentioned when discussing phishing letters is sometimes used on phishing pages, too. Every bit before long as a user opens the scam page, information technology begins a visible countdown of the time remaining for the credulous user to enter their data.
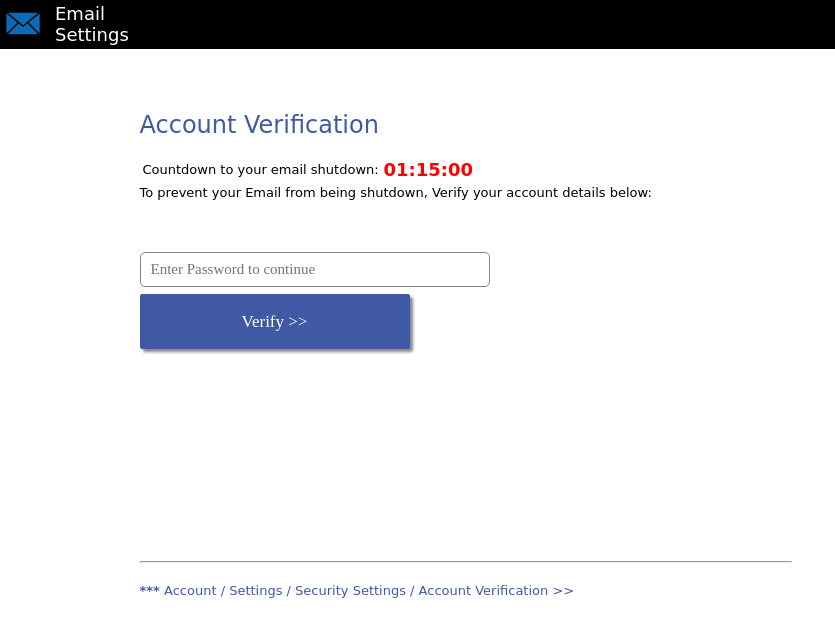
Some phishing pages, too, urge the user to brand haste
When a victim submits data through a phishing page, the results vary. Some websites plow inaccessible or return error messages. Others say the user entered incorrect data and ask them to effort again.
Probably the most dangerous scenario of all is gaining momentum of late. As soon every bit the information is submitted, the phishing page redirects the user to the real sign-in folio of the webmail service in question. The user figures there was a glitch, enters the login/password pair again, successfully this time, and forgets anything weird e'er happened.
Detecting phishing letters
- If the sender'southward address domain does not belong to the alleged sender's organization — and particularly if the mailbox is registered with ane of the free webmail services — the letter is a scam. Official mail always comes from official addresses.
- If the letter features links to click, unrelated domains, spelling errors, special symbols, and so forth, yous are looking at a fraud.
- If the letter says there are unexpected bug with your business relationship and demands y'all follow a link and log in before time runs out, that letter comes from scammers.
Information technology is useful just not strictly necessary to recollect all these things and pore over every letter yous receive. Instead, utilize a robust antivirus production to aid manage phishing and other online threats for you.
How Do Phishers Get Email Template,
Source: https://www.kaspersky.com/blog/email-account-stealing/28029/
Posted by: parmercombou1979.blogspot.com


0 Response to "How Do Phishers Get Email Template"
Post a Comment